When a company outsources its Proxmox backups, the temptation is strong to request root or admin access to the remote Proxmox Backup Server. After all, it's your backup, you want full control. Yet, that's precisely where the major risk lies.
At NimbusBackup, every client receives a backup-type account — not admin access. This isn't a limitation: it's a security architecture decision that protects your data even when everything else has been compromised.
Backup as a Service (BaaS) relies on a fundamental principle: the total separation between the entity that produces the data and the one that protects it.
1. Strong Segregation: Even When Compromised, Your Backups Survive
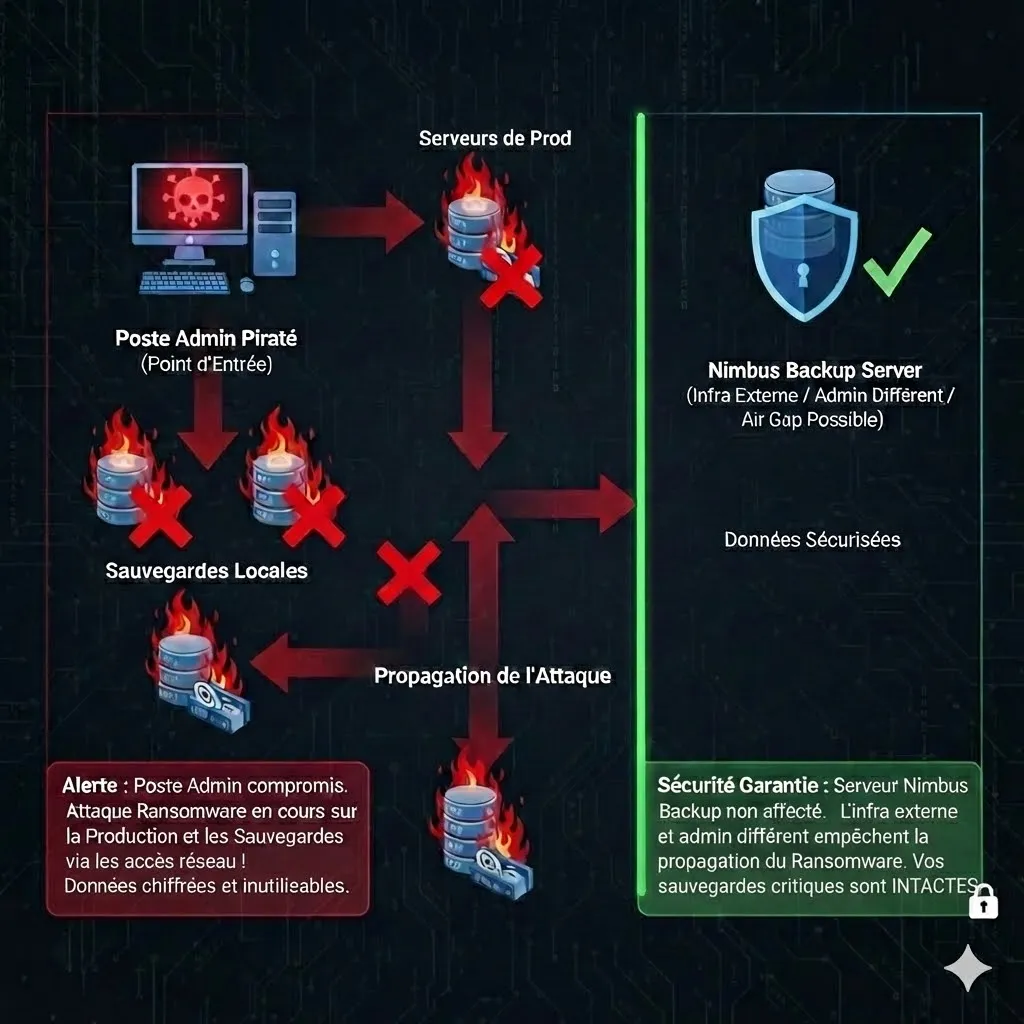
The worst-case scenario is no longer theoretical: ransomware encrypts your infrastructure, the attacker obtains admin credentials for your Proxmox VE servers. If they also hold PBS admin access, they can delete your backups before triggering the encryption.
In 2025, 96% of ransomware attacks specifically target backups (source: Veeam Data Protection Trends Report 2024). The #1 vector: shared admin credentials between production and backup.
With a backup-only account, even if the attacker compromises your entire IT environment — workstations, servers, hypervisors, Active Directory — they cannot:
What a backup account CANNOT do
- Delete a datastore
- Modify the retention policy
- Disable integrity verification
- Create/delete other users
- Access the underlying system (SSH)
- Modify network configuration
What a backup account CAN do
- Send backups (push)
- List its own backups
- Restore its own backups
- Verify its snapshot integrity
- View its operation logs
Result: even in case of total infrastructure compromise, your backups remain intact and restorable. That is the very definition of Backup as a Service.
2. Full Delegation: The Provider Stays Autonomous
When the client only has a backup account, the BaaS provider maintains full control of the underlying infrastructure. This isn't a detail — it's what guarantees service quality.
Scenarios Where Autonomy is Critical
Hardware Failure
A disk fails, the server needs replacement. The provider migrates data, reconfigures PBS, and the client only needs to update the fingerprint in PVE. Zero interruption to the backup chain.
Capacity Upgrade
Backup volume grows. The provider adds disks, migrates to a more powerful server or redistributes load — fully transparent to the client.
Security Patch
Critical patch on PBS or the underlying OS. The provider applies the fix immediately, without waiting for client validation, without risking breaking their configuration.
If the client had admin access, every infrastructure intervention would require coordination, negotiated maintenance windows, and the risk that a client configuration blocks the migration.
3. NIS2 / ANSSI Compliance: Zero Shared Admin Accounts
The European NIS2 directive (transposed into French law in 2024) and ANSSI recommendations impose strict requirements on access segregation for critical systems.
Requirements Met by the BaaS Model
"Access management and asset management" — No shared credentials between production and backup
"Business continuity and backup management" — Backup managed by an independent third party
At least 1 off-site copy, 1 offline copy, 0 verification errors — BaaS covers all 3
Each actor only has the rights strictly necessary for their function
The key point: in BaaS, there are absolutely no shared admin credentials between your infrastructure and the backup infrastructure. Even a compliance audit cannot fault you for shared privileges — there simply are none.
Read our complete NIS2 and backup guide4. Enhanced Anti-Ransomware Protection
Modern ransomware follows a 3-step playbook: (1) initial compromise, (2) lateral movement to locate and destroy backups, (3) encryption and ransom demand. Step 2 is where BaaS account segregation makes the difference.
Without BaaS (shared admin)
- ✗Attacker finds PBS credentials in PVE config
- ✗Connects as admin to the remote PBS
- ✗Deletes datastores or sets retention to 0
- ✗Backups destroyed before encryption
With BaaS (backup account)
- ✓Attacker finds backup credentials in PVE
- ✓Can list backups, but cannot delete them
- ✓Retention policy is out of reach
- ✓Backups intact, restoration possible
5. Principle of Least Privilege (PoLP)
The Principle of Least Privilege is a fundamental of IT security, well beyond NIS2. It states that each actor (human or machine) should only have the rights strictly necessary to perform their task.
For offsite Proxmox backup, the client's task is simple: send backups and restore them when needed. A backup account is sufficient. Giving admin access for this task is like giving the keys to the entire building to access one office.
PoLP isn't just a best practice — it's a prerequisite for most certifications (ISO 27001, SOC 2, HDS) and cyber insurance policies.
6. Zero Risk of Accidental Mishandling
Human error remains the leading cause of data loss. A well-intentioned administrator can accidentally:
- Delete a datastore thinking they're on the test environment
- Reduce retention from 30 to 3 days through a typo
- Run garbage collection at the wrong time
- Modify network configuration and lose PBS connectivity
With a backup account, these errors are structurally impossible. The client simply cannot access admin functions. Protection isn't based on discipline — it's based on architecture.
7. Cyber Insurance: A Coverage Criterion
Cyber insurers are tightening their conditions. Among the requirements that systematically come up:
Credential separation between production and backup
Off-site backup managed by an independent third party
Documented restoration tests performed regularly
Immutability or air-gap on at least one copy
The BaaS model with a backup-only account natively checks all these boxes. In case of an incident, your insurer cannot invoke a lack of access segregation to deny the claim.
8. Traceability and Audit Trail
Account separation creates a clear responsibility boundary:
Client Responsibility
- Backup job scheduling
- Choosing which VMs/CTs to back up
- Triggering restorations
BaaS Provider Responsibility
- Infrastructure availability
- Retention policy and garbage collection
- Automatic integrity verification
- 24/7 monitoring and alerts
During an audit (ISO 27001, NIS2, GDPR), this separation clearly demonstrates who does what, with distinct logs for each scope. No grey areas, no "but the admin did that".
Switch to Backup as a Service with NimbusBackup
Offsite PBS with segregated backup account, 24/7 monitoring, technical support included. From €12 excl. tax/TB/month.
How NimbusBackup BaaS Works
Provisioning
A dedicated datastore is created on our PBS infrastructure. A backup account (user@pbs) is generated with DatastoreBackup permissions only.
PVE Configuration
The client adds the remote PBS in Proxmox VE via Datacenter → Storage, with the provided fingerprint and credentials.
Automatic Backup
Backup jobs are configured in PVE. Backups automatically go to NimbusBackup PBS, encrypted in transit (TLS) and at rest (AES-256).
Monitoring & Alerts
NimbusBackup monitors infrastructure 24/7: disk space, job status, snapshot integrity. Automatic alerts on any anomaly.
NimbusBackup BaaS Plans
All our plans include a segregated backup account, 24/7 monitoring and technical support. The choice depends on your desired protection level:
Single Drive PBS
€12/TB/moBasic offsite backup. Entry-level BaaS protection.
Double Drive PBS
€19/TB/moGeo-replication across 2 sites. Best protection/price ratio.
AirGapped Drive PBS
€29/TB/moPhysical isolation against ransomware. Drives disconnected from the network.
Drive Bank PBS
€49/TB/moBank vault storage. Maximum physical security for critical data.
Frequently Asked Questions About Backup as a Service
What is Backup as a Service (BaaS)?
Backup as a Service is a model where a specialized provider fully manages the backup infrastructure: servers, storage, retention, monitoring and recovery. The client receives a "backup" type account (read/write backups) and not admin access to the underlying infrastructure.
Why not give the client admin access to PBS?
Admin access would allow deleting datastores, modifying retention policies or disabling integrity verification. In case of client IT compromise (ransomware, malicious access), the attacker would inherit these rights and could purge all backups. A backup account can only send and restore data.
Is BaaS compatible with the NIS2 directive?
Yes, and it's actually recommended. Article 21 of NIS2 requires security measures including access management and privilege segregation. The BaaS model with a backup-only account natively satisfies these requirements because no shared credentials exist between production and backup infrastructure.
What happens if the provider needs to change the PBS server?
This is actually one of the major advantages of BaaS. Since the client only has a backup account and no infrastructure access, the provider can replace, migrate or upgrade the underlying server (hardware failure, capacity upgrade) autonomously, with no client-side impact. The PBS fingerprint changes, but reconfiguration is seamless.
Backup as a Service vs self-hosted backup: what's the cost?
Self-hosted requires amortizing hardware (server, disks, UPS), paying for hosting, managing updates and 24/7 monitoring. BaaS mutualizes these costs. At NimbusBackup, PBS plans start at €12 excl. tax/TB/month with monitoring, alerts and support included.
Can I keep a local PBS in addition to BaaS?
Absolutely. It's actually the recommended setup in a 3-2-1 strategy: a local PBS for fast restores, and an offsite PBS in BaaS for off-site protection. Both are complementary.
How does restoration work in BaaS?
The client uses their backup account to restore directly from Proxmox VE, exactly as with a local PBS. Restoration can also be assisted by the provider in case of a major disaster (DRP). At NimbusBackup, technical support assists with every critical restoration.
Is BaaS accepted by cyber insurance providers?
Yes. Cyber insurers increasingly require strict separation between production and backup credentials. The BaaS model with a backup-only account, managed by a third party, precisely meets this requirement and is often a favorable criterion for coverage conditions.
