In 2025, ransomware attacks have reached unprecedented levels. According to the IBM Cost of a Data Breach 2024 report, the average cost of a data breach is now $4.45 million according to IBM. French companies are not spared: hospitals, local governments, industrial SMEs... No sector escapes this threat. Facing this reality, backup remains the last line of defense — but it must itself be unassailable. This is precisely the role of immutable backup.
What is an immutable backup?
An immutable backup is a copy of data that, once written, cannot be modified, deleted, or encrypted for a defined retention period. This concept is based on the WORM: Write-Once-Read-Many principle.
Concretely, when a backup is marked as immutable, even an administrator with root access to the storage system cannot alter the data. This guarantee is fundamental because modern ransomware systematically targets high-privilege accounts.
Two forms of immutability:
Software immutability
- - Object Lock (S3, MinIO)
- - Retention policies on the datastore
- - Write-protected snapshots
- - Firmware/software level protection
- - Flexible and programmable
Hardware immutability
- - WORM tapes (LTO WORM)
- - Non-rewritable optical discs
- - Physically non-modifiable media
- - Industry standard for legal archiving
- - 30+ year durability
An immutable backup guarantees that even an administrator with root access cannot modify or delete data during the defined retention period. It is this property that makes it effective against ransomware, which specifically exploits administrative privileges to destroy backups.
Why traditional backups are no longer enough
The ransomware of 2025-2026 has nothing in common with the first cryptolockers of 2017. Cybercriminal groups like Conti, LockBit, BlackCat (ALPHV) and their successors have developed sophisticated strategies that specifically target backup systems.
Anatomy of a modern attack:
1. Initial compromise (D-60 to D-90)
The attacker enters the network via phishing, unpatched vulnerability or exposed RDP access. They install persistent access and begin silent network reconnaissance.
2. Lateral movement and privilege escalation (D-30 to D-60)
The attacker identifies backup servers, NAS, storage spaces. They obtain admin credentials via tools like Mimikatz or Cobalt Strike.
3. Backup destruction (D-1 to D-7)
Before launching the final encryption, the attacker deletes or encrypts existing backups. Volume Shadow Copies (VSS), snapshots, backup directories are the first targets.
4. Encryption and ransom demand (D-Day)
Once backups are destroyed, the ransomware encrypts all production systems. Without a viable backup, the victim has no choice but to pay or rebuild everything.
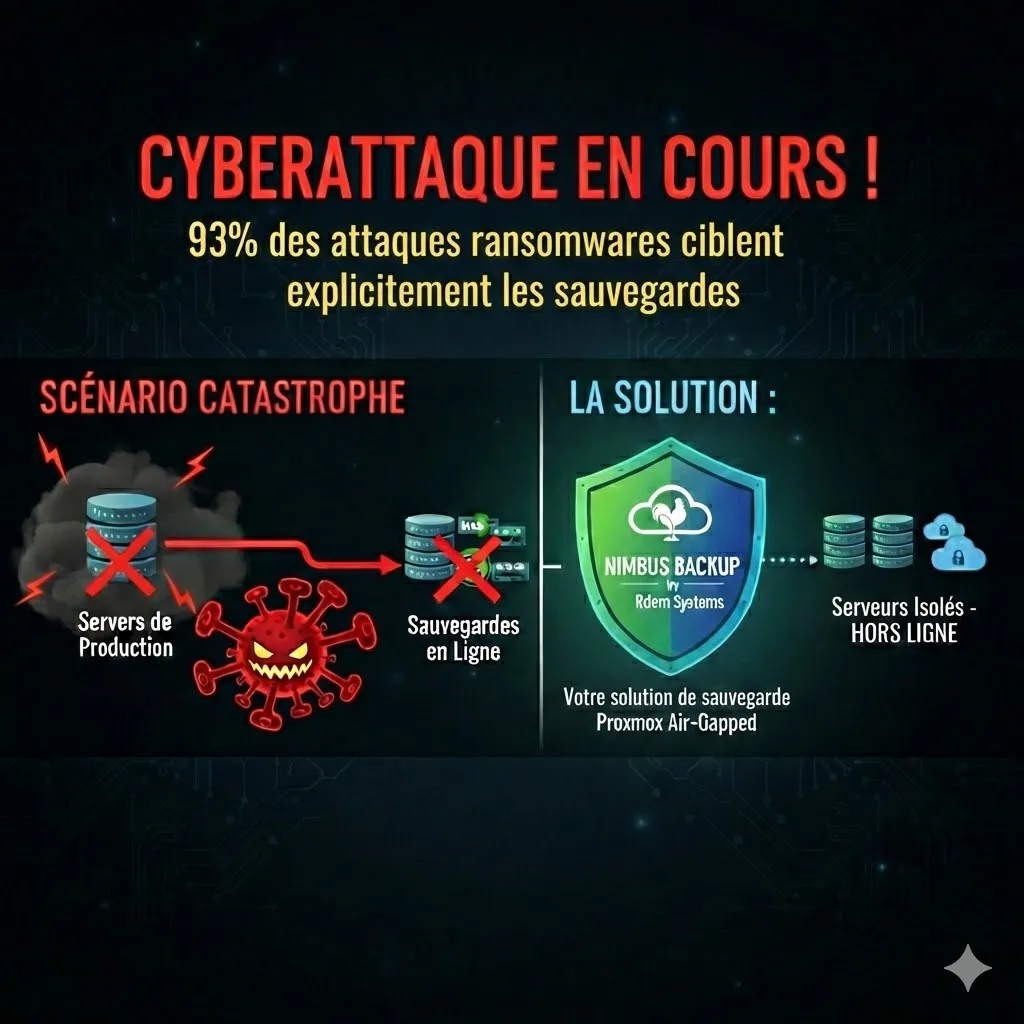
According to the Sophos State of Ransomware 2024 report, 94% of ransomware attacks attempt to compromise backups. Among organizations whose backups were targeted, 57% had their backups effectively destroyed. An online-accessible backup is a vulnerable backup.
Facing this situation, a "traditional" backup — even replicated to a second site — is no longer sufficient if it remains accessible via the network. Immutability or physical isolation (air-gap) become essential requirements for any serious protection strategy.
How immutability works in PBS
Proxmox Backup Server (PBS) natively integrates several mechanisms that contribute to protecting backed-up data against unauthorized modifications. While PBS does not implement a strict WORM lock in the regulatory sense, its architecture offers solid guarantees.
Datastore-level protection:
Client-side encryption (AES-256-GCM)
Data is encrypted on the source machine before transmission to the PBS server. The backup server never has the decryption keys. Even if the PBS server is compromised, the data remains unreadable and therefore unexploitable for an attacker.
Deduplication with integrity verification
PBS uses chunk-level deduplication with SHA-256 cryptographic fingerprints. Each block is verified on write and read, ensuring no silent alteration can go undetected.
Protected garbage collection
PBS's garbage collection mechanism protects chunks referenced by active snapshots. Only orphaned blocks (not referenced by any backup) can be deleted, preventing premature deletion of still-needed data.
Granular access control
PBS allows defining precise roles for each datastore: a backup account can write data without being able to delete existing snapshots, thus limiting the attack surface in case of account compromise.
Discover our hosted PBS solutions that combine these protection mechanisms with sovereign hosting in France.
Air-gapped vs immutable: two complementary approaches
In the field of backup protection, two approaches stand out: software/hardware immutability and physical isolation (air-gap). It is essential to understand their differences and complementarity to choose the strategy suited to your context.
Immutable backup (WORM)
- - Software or firmware lock on data
- - Data online, accessible for reading
- - Prevents modification even with physical access
- - Requires WORM-compatible media
- - Suited for strict regulatory requirements
- - Fast restore (data online)
Air-gapped backup
- - Physical network isolation
- - Disconnected disks or vault storage
- - No remote attack possible
- - Does not require specific WORM media
- - Pragmatic and proven protection
- - Longer restore time (reconnection needed)
Important: Our NimbusBackup Air-Gapped plans do not claim strict technical immutability (WORM). They offer equivalent — or even superior — protection against ransomware through physical isolation: a disk disconnected from the network simply cannot be encrypted remotely. This is a pragmatic approach that meets the real needs of most businesses.
In practice, air-gap is often considered a superior alternative to pure software immutability for ransomware protection. The reason is simple: software immutability relies on the reliability of the software implementing it. If a zero-day vulnerability is discovered in the storage system, the software WORM lock can theoretically be bypassed. A physically disconnected disk, on the other hand, is fundamentally inaccessible — no software vulnerability can bridge a physical air-gap.
Our plans combining these approaches:
Our AirGapped Drive PBS plan uses physical disk rotation: one set of disks connected for backup writing, a second set disconnected and stored offline. Regular rotation ensures at least one copy is always physically inaccessible from the network.
The Drive Bank PBS and Magnetic Bank PBS plans add bank vault storage to this physical isolation. Backup media (hard drives or LTO tapes) are deposited in a secure bank vault, creating an additional physical barrier against any unauthorized access — including by a malicious employee with access to technical premises.
LTO tape archiving (Magnetic PBS) offers 30+ year durability with 12 TB native capacity per cartridge (LTO-9). Magnetic tapes, by nature offline when not in the drive, constitute an inherent form of air-gap while offering an unbeatable cost/capacity ratio for long-term archiving.
Checklist: implementing an immutable backup strategy
Whether you opt for software immutability, physical air-gap or a combination of both, here are the essential steps to deploy a ransomware-resilient backup strategy. Check our article on the 3-2-1-1-0 rule and best practices to deepen these concepts.
Anti-ransomware protection checklist
Warning: A backup that has never been restore-tested is not a backup — it's a hope. Restore tests must be planned, executed and documented at least once per quarter, under conditions as close as possible to a real disaster scenario.
NimbusBackup solutions: quasi-immutable protection through physical isolation
Our PBS backup plans are designed to offer maximum protection against ransomware by combining client-side encryption, verified deduplication and physical isolation. While we do not claim strict WORM immutability, our air-gap approach guarantees concrete and proven protection against attacks. These solutions also meet the requirements of the NIS2 directive.
Single Drive PBS - 12 EUR/TB
Encrypted backup on a dedicated server. Ideal entry point for a first layer of PBS protection with AES-256 encryption.
Double Drive PBS - 22 EUR/TB
Geo-redundancy across 2 separate sites. Protection against datacenter loss with automatic replication.
AirGapped Drive PBS - 34 EUR/TB
Physical disk rotation with air-gap isolation. One copy is always disconnected from the network, out of ransomware's reach.
Drive Bank PBS - 69 EUR/TB
Air-gapped disks deposited in a bank vault. Double isolation: physical (disconnection) and geographic (secure vault).
Magnetic PBS - 89 EUR/TB
HDD + automatic LTO tape archiving. 30+ year durability, ideal for regulatory compliance and long-term archiving.
Magnetic Bank PBS - 149 EUR/TB
Maximum protection: 2 sites + LTO tapes in bank vault. Maximum compliance for critical and regulated entities.
Features common to all our plans:
- - AES-256-GCM client-side encryption (you alone hold the keys)
- - European hosting, French on request (AS206014)
- - SHA-256 deduplication and integrity verification
- - Monitoring and alerts included
- - French technical support
Conclusion: don't let your backups become the target
In 2026, the question is no longer whether your organization will be targeted by ransomware, but when. The statistics are clear: virtually all attacks now target backups first. A backup strategy that doesn't account for this reality is an incomplete strategy.
Immutability — whether software (WORM) or physical (air-gap) — transforms your backups from an easy target into an impenetrable shield. The choice between these two approaches depends on your context: WORM immutability suits environments with strict regulatory constraints, while air-gap offers pragmatic and often superior protection against remote attacks. To learn more, check our guide on multi-site DRP with PBS. For proactive incident detection, discover our 8 essential server monitoring KPIs.
Investing in immutable or air-gapped backup is not a cost — it's insurance. The cost of a disconnected disk is negligible compared to the $4.45 million average cost of a data breach. Protect your backups today, before it's too late.
Sources and references
Protect your Proxmox VMs with NimbusBackup
Offsite, immutable and sovereign backup. Starting at 12 EUR/TB/month.
